Black Friday and Cyber Monday compress an extraordinary amount of business activity into a single week. U.S. holiday sales are expected to surpass $1 trillion in 2025, with nearly half of annual online revenue concentrated in this short window. When that much revenue flows through checkout systems, APIs, and third-party services at once, the cost of disruption rises sharply.
The reality is simple: if the holiday season contributes a significant portion of revenue, then security prioritization, budget allocation, and operational readiness should reflect that seasonality. Retailers need clarity on where their exposure is highest, what their likely attack paths are, and which targeted remediation actions can meaningfully reduce risk when the business is running at peak velocity.
Why Black Friday and Cyber Monday Create a Perfect Storm
During Black Friday and Cyber Monday, operational load and attacker intent rise at the same time, creating ideal conditions for exploitation. Retailers face compressed fulfillment windows, aggressive traffic spikes, and heavy dependence on third parties, increasing system complexity at the exact moment when uptime is most critical.
This amplification of exposure is made worse by a long-standing structural gap: according to the CYE Cybersecurity Maturity Report 2025, more than 75% of companies still lack full visibility into their IT assets, dependencies, and external connections. That blind spot becomes far more costly during peak season, when a single vulnerable integration, misconfigured API, or unmonitored endpoint can become the entry point for account takeover, injection attacks, or operational disruption.
Attackers understand the timing as well as the incentives. Holidays and weekends consistently see higher ransomware and extortion activity, as response teams are stretched thin and the financial leverage is greater. As revenue and operational pressure peak, the business impact of even a brief outage multiplies, making these days some of the most attractive targets of the year.
Retail Attack Patterns During Peak Season
During Cyber Week, attackers focus on the weaknesses most likely to yield results when systems are under strain and customers are rushing to buy. Several patterns stand out:
- Bot-driven activity surges, with credential stuffing, account takeover attempts, and automated carding often increasing 2 to 3 times during major sales events.
- Client-side attacks expand, including Magecart-style skimming and malicious JavaScript injections that take advantage of rapidly updated promotional pages and overloaded release pipelines.
- API and business logic abuse accelerates, from inventory-hoarding bots to coupon manipulation and race-condition exploits in cart and checkout flows.
- Ransomware and extortion timing becomes strategic, targeting the narrow window when downtime has the highest financial impact.
- GenAI-enhanced social engineering becomes harder to detect, particularly when attackers mimic internal communication patterns or exploit holiday urgency.
Instant Visibility With the Industry Attack Graph
While these threat types are well documented, security teams typically have to run assessments, configure connectors, and wait for scans to complete before they see anything meaningful or specific to their industry or organization – leaving them without immediate visibility into the most likely attack routes in retail.
That context is essential because teams can’t fix everything, especially when systems are operating at peak capacity and the impact of downtime is highest. Prioritizing by technical severity alone offers little insight into how attackers are most likely to move through retail environments or which threats would carry the greatest business impact.
CYE’s Industry Attack Graph fills this gap by giving retailers day-one visibility into the most common attack routes observed across the sector. It highlights the threat sources and paths most frequently used against retailers’ business-critical assets, giving teams the clarity and context they need to cut through the noise.
A mapped view of the attack paths most active in the retail industry
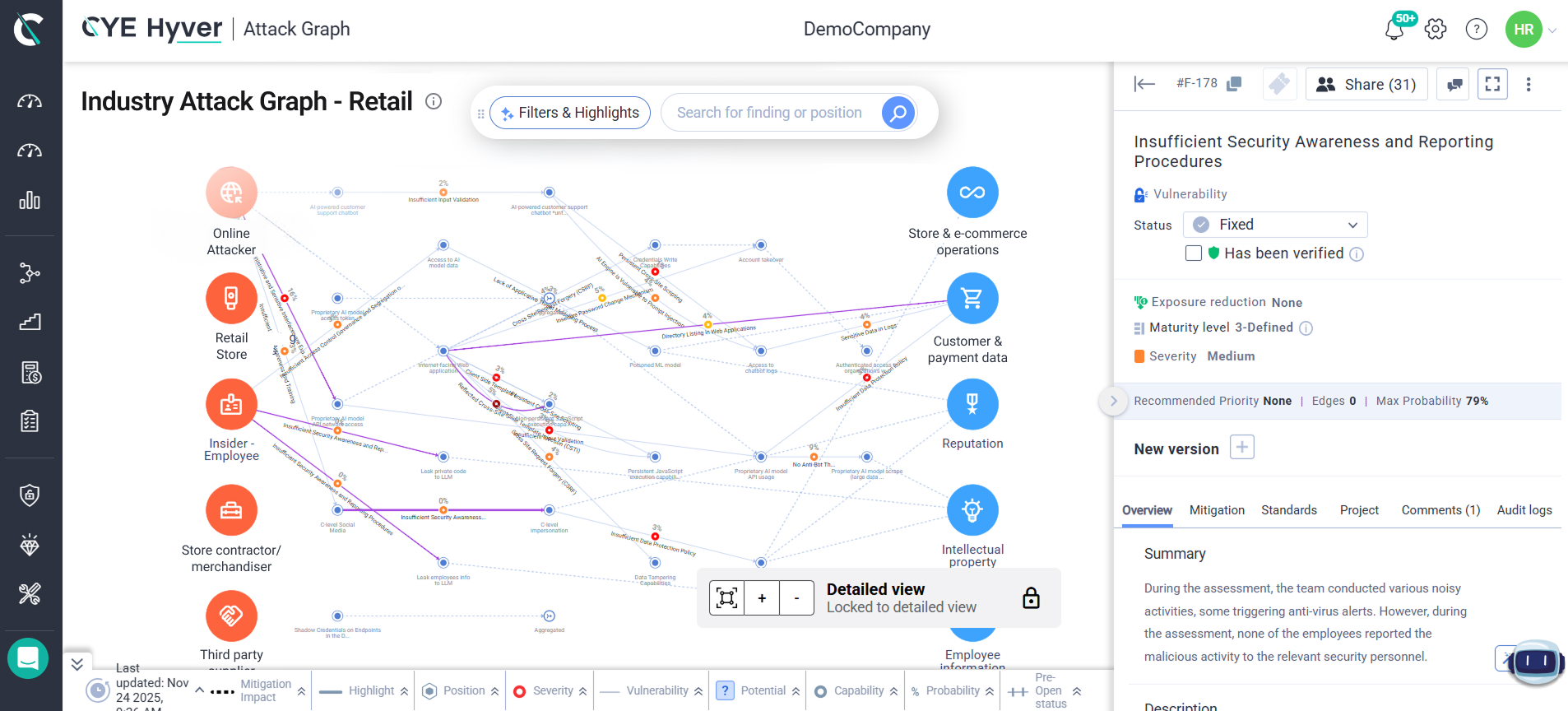
Retailers can also add their own data and instantly see how it maps onto these industry-level attack routes. All it takes is a simple file upload (PDF, CSV, etc.) into the platform, and CYE’s AI-driven engine automatically maps the findings onto the attack graph.
The result is a clear, estimated view of the attack paths and findings most relevant to their environment, so security teams can prioritize and focus their limited time and resources on the most probable routes and threats.
How to Mitigate Exposure in High-Traffic Windows
The objective during high-traffic windows is precision: focusing effort where it measurably reduces exposure without destabilizing the systems that carry the bulk of seasonal revenue.
Here are the actions that make a meaningful difference during peak-season traffic:
- Reinforce identity controls on high-value systems such as IAM, SSO, admin portals, and payment interfaces, where compromised credentials frequently sit on common attack paths.
- Harden client-side code paths for checkout and payment flows to reduce exposure to skimming, injection, and malicious JavaScript that often targets rapidly updated promotional pages.
- Increase visibility into API behavior, especially for cart, promotions, pricing, and inventory endpoints that attract bot-driven abuse and logic attacks during sales events.
- Validate critical third-party integrations, including payment gateways, anti-fraud tools, CDNs, and shipping APIs, for unusual patterns or degraded performance.
- Tune detection and alerting to align with seasonal indicators such as bot surges, credential stuffing spikes, anomalous login velocity, and rapid session creation.
- Use out-of-band verification for operational or financial approvals to counter GenAI-driven impersonation and urgent holiday-themed social engineering.
- Use the Industry Attack Graph and overlay your findings to quickly see your organization’s estimated attack routes so you can prioritize by path risk and probable impact.
Invest in Seasonality – Context Is King
Black Friday and Cyber Monday concentrate revenue like no other moment in the retail year. When nearly half of annual sales occur within a matter of days, cyber risk no longer behaves as a constant. Exposure rises, attacker incentives spike, and the business impact of even a brief disruption multiplies.
Security programs need to reflect that reality. Retailers benefit most when prioritization, budget decisions, and operational readiness adapt to the seasonality of their business, focusing effort where it has the greatest influence on actual attacker movement.
When teams understand the most probable attack paths and routes to their business-critical assets, and which remediation actions meaningfully reduce the likelihood and impact of attacks, they can turn seasonal pressure into a data-driven advantage rather than a point of fragility.
If most of your revenue happens in one week, make sure most of your resilience does too. See how attackers potentially move in your industry with CYE’s Industry Attack Graph and prepare your organization for the days when the margin for error is smallest.










